What Endfield’s Payment Incident Reveals About the Hidden Risk of DTC Monetization
On launch day, players of Arknights: Endfield weren't just charged for their own purchases - they were charged for other players' purchases too. The technical post-mortem reveals a cautionary tale for any publisher building direct-to-consumer payment infrastructure.
What Happened
On January 22, 2026, Hypergryph launched Arknights: Endfield, the highly anticipated action-RPG spin-off of the popular tower defense game Arknights. Within minutes of global release, something went terribly wrong.
Players attempting to purchase in-game items through PayPal began reporting bizarre charges. One user tried to buy a battle pass and was charged thousands of dollars instead. Another nearly faced a $1,200 charge that cycled through multiple currencies, USD, JPY, and Canadian dollars, none of which matched their account. On Reddit, a player posted a screenshot showing charges exceeding €13,000 EUR.
The charges weren’t just incorrect - they were appearing on other players’ PayPal accounts. Users who had completed purchases early after launch found themselves repeatedly billed for transactions they never initiated.
Within the first hour, Hypergryph disabled PayPal payments entirely. Refunds followed, but for many players, the damage, financial and reputational, was already done.
In the days that followed, a detailed technical analysis circulated within Chinese payment-industry circles. That analysis framed responsibility overwhelmingly on the merchant side: roughly 90% attributed to Hypergryph’s payment architecture, with the remainder tied to how PayPal’s systems behave when merchant-side safeguards fail under extreme concurrency.
Why This Wasn't a Freak Accident - And Why the Risk Is Growing
The Endfield incident wasn’t caused by a sophisticated attack or an obscure edge case. It was the result of basic payment-safety guarantees breaking down under real-world launch conditions.
At a high level, the system failed to enforce a simple rule: a payment authorization should only ever be usable by the user who created it, and only for the transaction it was intended for. Under launch-day concurrency, authorizations were not tightly bound to individual users or sessions, allowing them to be reused across requests - sometimes across users.
The result was repeated charges for early purchasers and unexpected charges appearing on unrelated accounts. With no effective way to prevent repeated execution or quickly surface abnormal patterns, the issue persisted long enough to impact many players.
Crucially, this wasn’t an exotic failure.
The same conditions that enabled it are becoming more common across the industry:
- Direct-to-consumer monetization pushes publishers to build and operate their own payment infrastructure.
- Global, day-one launches create traffic patterns that are difficult to fully simulate in advance.
- An expanding mix of payment methods increases system complexity with every new integration.
- Delivery pressure often favors performance and speed over strict correctness guarantees.
- Rising regulatory and compliance demands raise the cost of getting payments wrong.
The uncomfortable reality is that these trade-offs are common, but when payment infrastructure fails, it rarely fails gracefully - and the cost is measured not just in refunds, but in player trust.
What Safe DTC Payment Systems Actually Require
The Endfield incident wasn’t caused by a single mistake - it was the result of several basic payment guarantees failing at once. Any direct-to-consumer payment system, regardless of provider or scale, should be able to uphold the following:
The Non-Negotiables
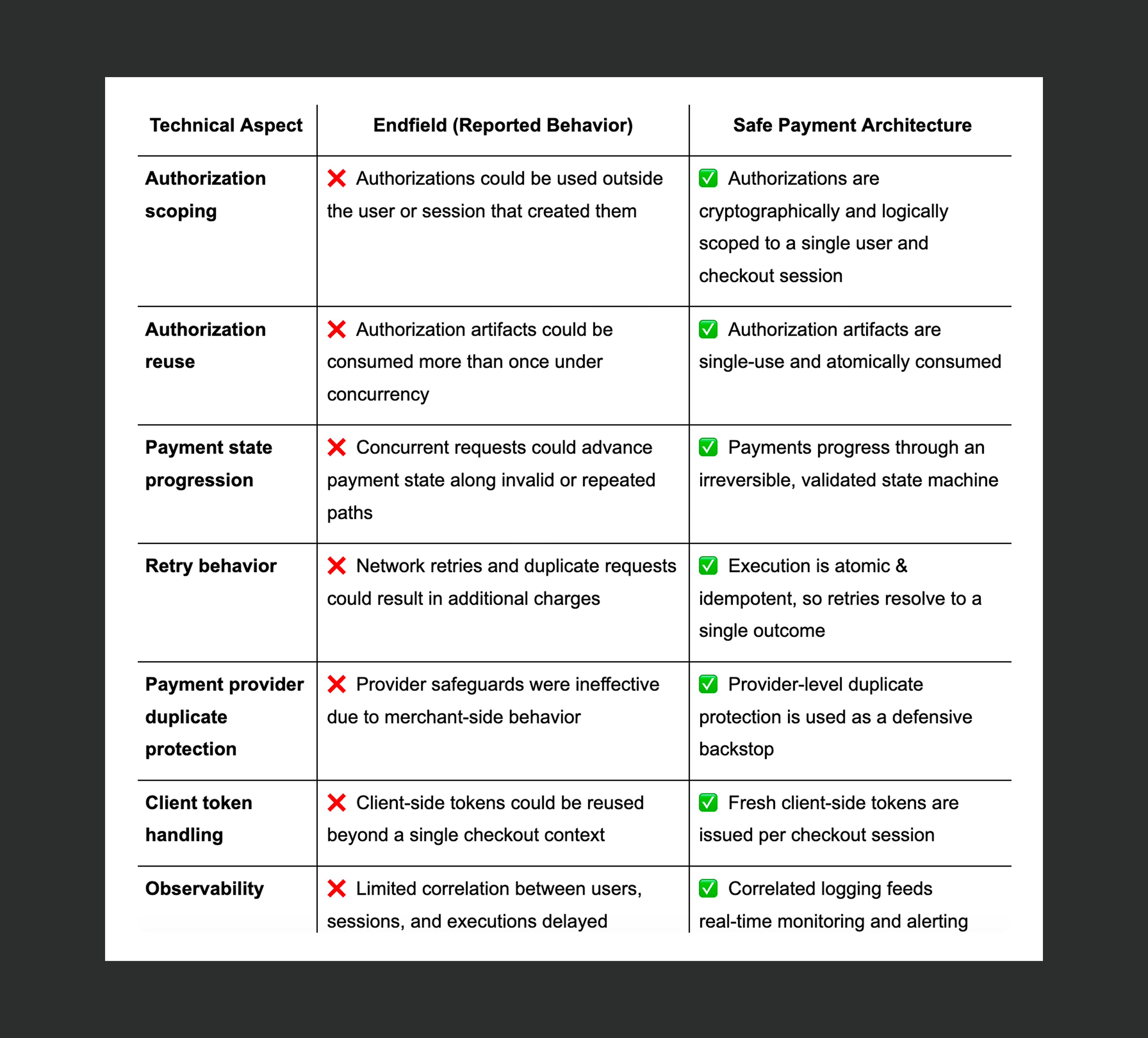
Session-scoped authorization
Every checkout session must generate a fresh, cryptographically unique authorization from the payment provider. Authorization credentials should never be stored in shared server-side pools. Each authorization exists only for its intended user and transaction.
Single-use payment tokens
When a user authorizes a payment, the provider should return a one-time-use token bound to that specific session. That token must be consumed atomically on first use and must not be reusable for any other transaction - by design.
Deterministic payment state machine
Every payment must progress through a strictly defined, irreversible state machine. Each state transition must be validated against the initiating user and the intended transaction, and must be applied atomically. Invalid or repeated transitions should be rejected by the system itself, not handled implicitly in application logic. Under concurrency, incorrect state transitions must be structurally impossible - not merely rare.
Idempotent payment execution
Retries, timeouts, and duplicate requests are inevitable, especially under launch-day load. Each payment must have a stable, unique identity, while every execution is treated as an atomic attempt against that identity. Repeated attempts for the same payment must always resolve to the same outcome, never trigger additional charges, and never advance the payment beyond its intended state.
Auditability and real-time monitoring
Payment systems must maintain a complete, queryable audit trail linking users, sessions, orders, and provider authorizations. Equally important, those signals must feed real-time monitoring so that abnormal behavior is detected quickly. When something goes wrong, affected users should be identifiable within minutes, not hours.
Technical takes: Endfield vs. Safe Payment Architecture
Here’s how the reported Endfield implementation compares to common payment-system patterns used to enforce safety guarantees at scale.
Beyond Architecture: The Expertise Gap
The deeper lesson from the Endfield incident is that it wasn’t just an architectural failure - it was an operational one.
Hypergryph is a game studio. Their strengths lie in game design, live operations, and player engagement. Payment infrastructure, by contrast, is a financial system that must behave correctly under failure, concurrency, and partial success - conditions that are easy to underestimate until something goes wrong.
This is the hidden risk of in-house direct-to-consumer payment systems. Even if the initial architecture is sound, sustaining payment safety over time requires a different kind of discipline than most product teams are set up for.
It means consistently validating behavior under real-world concurrency, not just functional correctness. It means pressure-testing new payment methods and providers before launch, and re-validating assumptions as systems evolve. It means maintaining the same safeguards as traffic patterns change, markets expand, and regulatory requirements shift. And it means having the visibility and response processes to detect issues early, before they cascade into player-facing incidents.
These are not one-time engineering tasks. They are ongoing operational responsibilities - closer to running financial infrastructure than shipping application code.
This is why many studios ultimately reconsider how much payment infrastructure they want to own directly. Some choose to build and operate it themselves, investing heavily in fintech expertise and process. Others partner with teams whose primary focus is payments, so their own engineering effort can remain centered on building games.
At companies such as Appcharge, payments are the core focus. We spend our time on exactly these operational challenges, maintaining safeguards across providers, handling real-world concurrency, and adapting as systems and regulations change - so studios don’t have to turn payments into a secondary core competency.
The Takeaway
The Arknights: Endfield incident will likely be remembered as a cautionary moment for the gaming industry. But the more important lesson isn’t about one company’s mistake, it’s about how fragile payment systems can become when things don’t work out as planned.
As direct-to-consumer monetization expands, more publishers are taking on the responsibility of building and operating their own payment infrastructure. With that shift comes exposure to failure modes that don’t surface in functional testing, but emerge under real traffic, real money, and real pressure. Not to mention a poor experience for players.
Payment safety isn’t something you add at the end of a development cycle. It isn’t a checklist item or a one-time integration. It’s an ongoing discipline that depends on correct architecture, operational rigor, and sustained expertise.
For game studios, the real question isn’t whether payment infrastructure can be built in-house - it’s whether that’s where you want your engineering focus to live, or whether that energy is better spent on what you do best - building great games.